Architectural workflow
This topic describes the traffic flow and security enforcement for mobile devices using the Mobile Endpoint Agent.
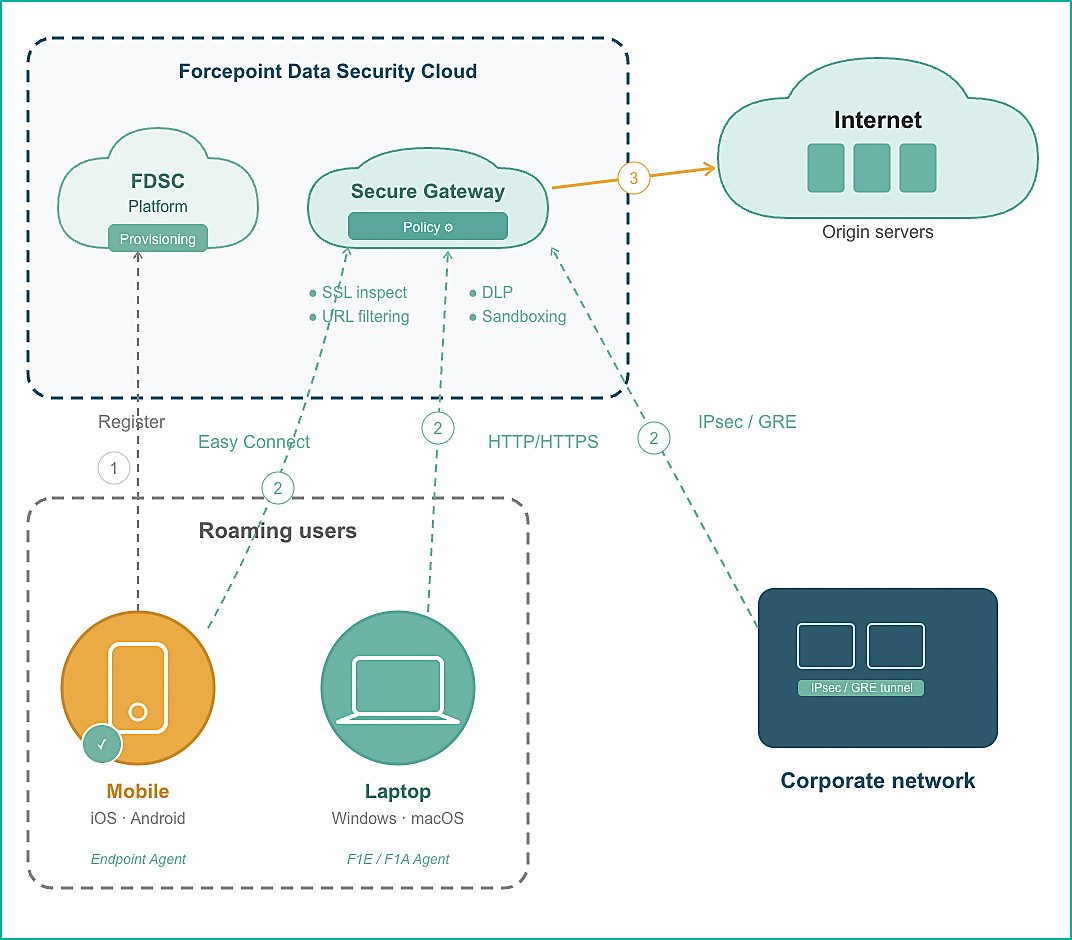
- Device Registration and Provisioning: When the Mobile Endpoint Agent is installed on a managed mobile device, it registers with the Forcepoint Data Security Cloud. During this process, the device is provisioned with the required configuration and identity that allow it to securely communicate with Forcepoint
cloud services.
This registration ensures the device is recognized as a trusted endpoint and is subject to the organization’s defined security policies.
-
- Secure Connectivity from the Mobile Device: Once registered, the Mobile Endpoint Agent establishes a secure connection to the Secure Gateway. This connection allows roaming users to maintain security regardless of the network they are connected to, whether it's home Wi-Fi, public networks, or mobile data.
- Traffic Ingestion into the Secure Gateway: All outbound web traffic from mobile devices is routed through the Secure Gateway in the Forcepoint Data Security Cloud. At this point, the traffic from mobile devices is managed in the same way as traffic from other protected endpoints, such as laptops. This unified approach ensures consistent handling of all traffic and eliminates the need for separate policies specifically for mobile devices.
- Policy Enforcement and Inspection: Inside the Secure Gateway, traffic is managed according to the organization’s established policies. This includes:
- URL filtering
- SSL inspection
- DLP & content scan
- Threat detection and sandboxing
Since both mobile and desktop endpoints utilize the same policy framework, existing security configurations automatically extend to mobile devices without requiring any additional setup.
- Alignment with Corporate Network Traffic: For users connected to the corporate network, traffic may also flow through secure tunnels (such as IPsec or GRE) into the Secure Gateway. This ensures consistent inspection regardless of whether the device is on‑network or off‑network.
Mobile devices, laptops, and corporate network traffic all converge at the same security enforcement point, maintaining a unified security model.
- Controlled Access to Internet Resources: After policy evaluation and inspection, traffic is sent from the Forcepoint cloud to the intended internet origin servers. If traffic violates
policy, it is blocked or handled according to the defined enforcement actions.
This ensures that corporate security controls remain in effect even when users access the internet from outside the corporate environment.