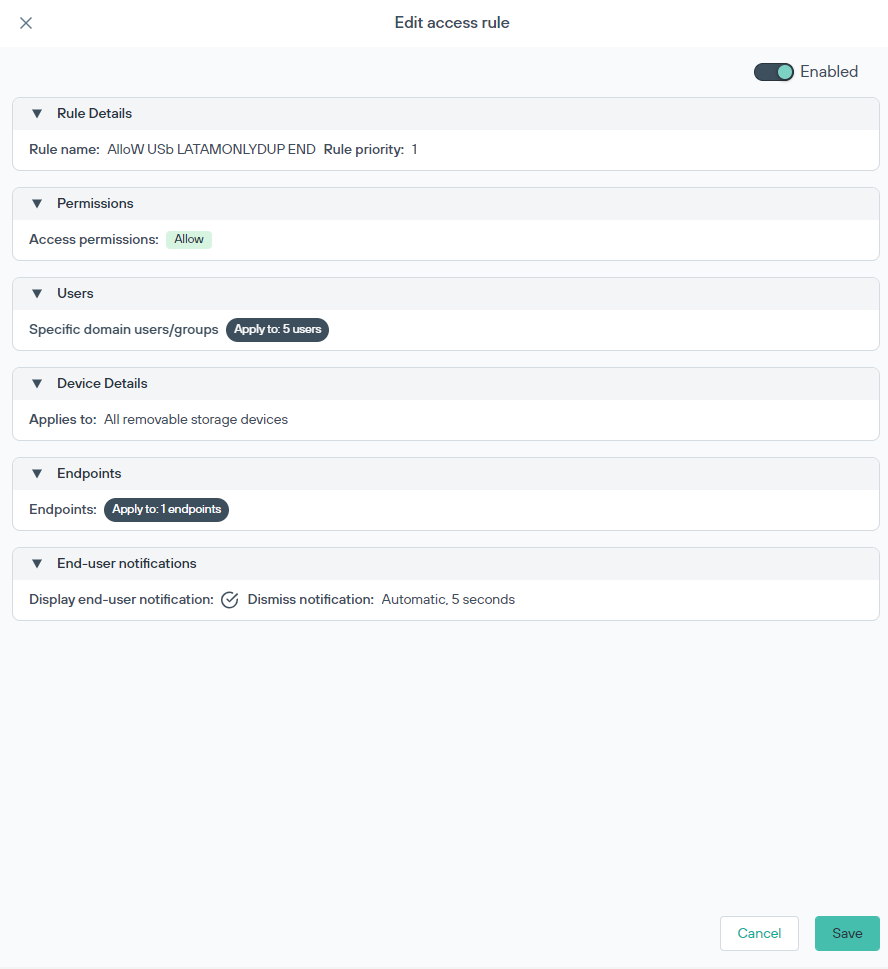
Edit access rule
Previously created access rules can be edited.
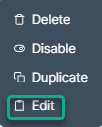
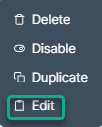
Right-click on the specific access rule and select Edit to open the access editor.
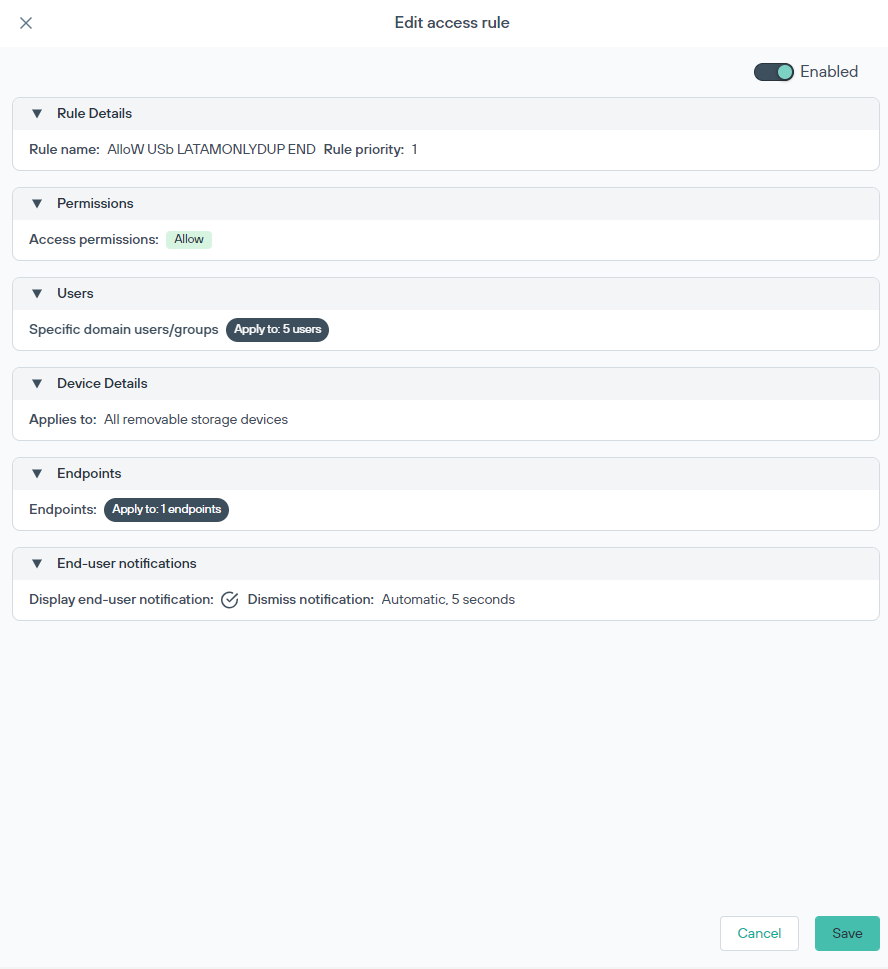
Previously created access rules can be edited.
Right-click on the specific access rule and select Edit to open the access editor.